Approx. 4 years ago on April 25, 2018, Peter Wood (at that time CEO of First Base Technologies, LLP) has published an excellent introduction into the topic „Information Security as business enabler“ in the ISACA Now blog:
„The business landscape has changed beyond recognition since I started working, way back in 1969. Every business is now reliant on IT systems and the Internet in order to function (just see what happens if your email systems are unavailable for an hour!). New technologies and working practices are introduced at a prodigious rate, as globalization and consumerization drive transformation and innovation.
As a result of our dependence on IT systems and connectivity, information and cybersecurity are being pushed up the corporate agenda. This is a good thing. However, information security and its practitioners are still seen as risk-averse business inhibitors who stifle innovation, limit agility and slow efficiency with their strict controls and policies.
Meanwhile, information security teams grapple with the challenges of securing increasingly complex and ever-changing threat landscapes, while attempting to secure increasingly diverse and poorly-understood sets of technologies.“
So far, so bad. Since 2014, the need for action has become even bigger. 2017 was a nightmare year for security according to a professional report provided by riskbasedsecurity.com on January 3, 2018. In fact, 2017 was the worst year on record for frequency and severity of data breaches as well as the most vulnerabilities disclosed that we’ve ever seen due to the following facts:
- As of December 31, there were over 5,000 publicly disclosed data breaches in 2017. Without a doubt that makes it the worst year in terms of frequency, as the previous highest year was 4,190. This brings the all-time total up to over 28,800 data breaches.
- When the third quarter DataBreach QuickView Report was published, it had already been the worst year ever recorded in terms of the amount of records exposed. There has been 7.8 Billion records exposed thus far. The previous highest was 2016 as well, and that was originally 4.3 Billion, but just recently upped to 6.3B due to Yahoo! updating their breach. This now brings us up over 19+ Billion records exposed all time.
- When looking at the software that organizations rely on, there were over 20,000 vulnerabilities disclosed in 2017. Last year there were 15,866 disclosed vulnerabilities, a 25.5% increase in reported weaknesses.
Since data breaches and other Information Security and Data Privacy incidents can seriously damage the reputation and trustworthiness of enterprises, corporates all around the world spend more than hundred billions dollars per year to ensure an adequate level of Information Security and Data Privacy for their businesses. Worldwide spending on information security products and services will reach over $114 billion in 2018, an increase of 12.4% from last year, according to the latest forecast from leading research firm Gartner (source: Forbes.com article on „Global Information Security Spending To Exceed $124B In 2019, Privacy Concerns Driving Demand“ published on August 19, 2018).
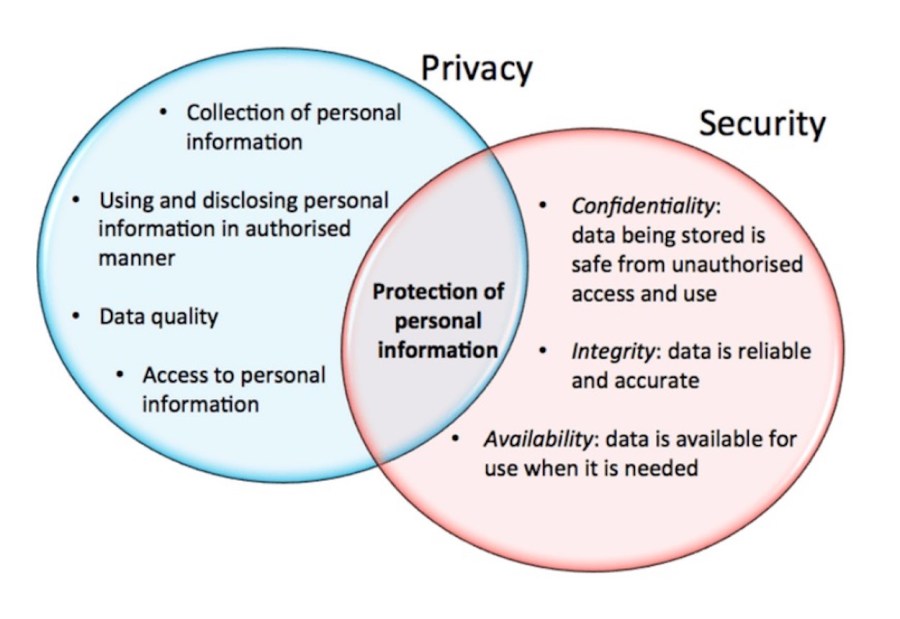
For those of you not being familiar so far with both terms, I would like to provide the following short definitions.
Information Security (InfoSec) is the practice of preventing unauthorized access, use, disclosure, disruption, modification, inspection, recording or destruction of information. The information or data may take any form, e.g. electronic or physical. Information security’s primary focus is the balanced protection of the confidentiality, integrity and availability of data (also known as the CIA triad) while maintaining a focus on efficient policy implementation, all without hampering organization productivity (source: Jason Andress, „The Basics of Information Security: Understanding the Fundamentals of InfoSec in Theory and Practice“ published on June 9, 2014).
Information Security should not be mixed up with Data Privacy.
Data Privacy concerns the right of a person to informational self-determination, i.e. the protection of the person against unauthorized use of information about him-/herself, for example by intentional or unintentional processing of personal data. Essentially, the concept of processing includes collecting, gathering, organizing, sorting, storing, adapting or modifying, reading, querying, using, disclosing through transmission, dissemination or any other form of providing matching or linking, restriction, deletion or annihilation (source: Kurt Brand, „General Protection Regulation (GDPR) comprehensible: what the new EU rules mean for citizens“ published on May 27, 2018)
Simplified illustration:
While most people will probably agree, that confidentiality, integrity and availability of business-related data as well as informational self-determination of customers and employees are important for almost any kind of business and almost any citizen using the internet – particularly in today’s data-driven era of digitalization and digital platform economy – the related topics of Information Security and Data Privacy are widely considered as sexy as loss of hair, beer belly or foot fungus.
This has to do not least with the defensive definition of both topics focussed on preventing misuse, the technology orientation and the cryptic language, which is very commonly used in both topics. Unfortunately, it is (far too) often ignored that both Information Security and Data Privacy can play as well an important role as business enabler.
Some major examples:
- Public Key Infrastructure (PKI) which is mostly used for email encryption purposes can as well be leveraged to implement electronic workflows, which improve the productivity of an enterprise, based on digital signatures.
- Information Security can help the business to improve internal collaboration as well as collaboration with with suppliers and with customers.
- When a team incorporates security throughout its agile process, the benefits gained are for example a higher confidence in what is released into production or a faster reaction to making improvements or fixes.
- Authentication, authorization and accounting (AAA) tools give network users a rich identity for enforcement of the organization’s security policies all with a single password, certificate, key fob or fingerprint.
- Blockchain technology is a key technology for the future networking of „things“ on the Internet of Things – securely, reliably, transparently and cost-effectively.
- InfoSec related information can be used to improve prioritization of investments in your IT infrastructure by gaining a better understanding of who and how many people are using specific IT-services and applications.
- Geo-location data of your customers can be utilized to optimize your advertising efforts while at the same time questioning unusual communication patterns to determine if the behavior is marketing-oriented or malicious.
- Security tools can deliver detailed information to shape your content marketing strategy, such as information which social media outlets are most relevant to your employees or customers.
- With security solutions such as mobile device management (MDM), organizations can enable enhanced mobile productivity while maintaining full security and compliance.
Besides the still necessary and reasonable risk-orientation, Information Security and Data Privacy professionals need to learn as well to think in chances and put benefits of both topics for the business in their argumentation much stronger in the foreground.
This requires adequate staffing of the Information Security and Data Privacy function in a corporation. The times in which these functions were used as an elephant cemetery for non-specialist employees who had passed the zenith of their career should be finally over.
Peter Wood closes his introduction into „Information Security as business enabler“ from April 25, 2018, with the following conclusion, I fully concur with:
„With heightened attention at the board-level, information security professionals have an opportunity to reimagine information security as an enabling function, supporting and adding value to the business as it transforms and innovates. The challenge for many security people is that their passion and enthusiasm can be difficult to communicate to the senior level. We are asked to present arguments in a language business leaders can understand – to remove technobabble from our presentations. Oftentimes we struggle to properly express our concerns and we fail to engage these audiences.
Our information security functions must evolve to become business-led. We must bring business knowledge to security teams and educate security practitioners about the implications of threats. The perception of risk within information security must be changed. Information security must get management/stakeholder buy-in and become fundamental to enterprises, rather than a mere compliance issue. And the language used in this process must improve to ensure effective communication of risk intelligence without instilling fear, uncertainty and doubt.“
As always, I am grateful for your thoughts and feedback on the considerations provided in this blog.
Finally I would like to recommend three complementary blogs to you:
- How the U.S. government discredits the U.S. American IT industry you can learn in my blog of the same name published on August 20, 2017: https://kubraconsult.blog/2017/08/20/how-the-us-government-discredits-the-us-american-it-industry/ (German version: https://kubraconsult.blog/2017/03/08/wie-die-us-regierung-das-internet-diskreditiert/).
- Why Smartphones are an ideal tool to spy on you, your family&friends and your colleagues is explained in my blog „The spy in your pocket“ published on April 25, 2017: https://kubraconsult.blog/2017/04/25/thy-spy-in-your-pocket/ (German version: https://kubraconsult.blog/2017/04/25/der-spion-in-ihrer-tasche/).
- What the new rules of the General Date Protection Regulation mean for EU citizens can be read in my blog of the same name published on May 27, 2018: https://kubraconsult.blog/2018/05/27/general-protection-regulation-gdpr-comprehensible-what-the-new-eu-rules-mean-for-citizens/ (German version: https://kubraconsult.blog/2018/05/04/datenschutz-grundverordnung-dsgvo-verstaendlich-was-die-neuen-eu-regeln-fuer-die-buerger-bedeuten/).
- A comprehensive introduction into „Digital business models and Platform Economy“ and the related Information Security and Data Privacy risks is provided in my blog published on November 4, 2017: https://kubraconsult.blog/2017/11/04/digital-business-models-and-platform-economy/ (German version: https://kubraconsult.blog/2017/09/06/digitale-geschaeftsmodelle-und-plattformoekonomie/).
8 Kommentare zu „Reframing Information Security and Data Privacy as Business Enabler“